What is Email Spoofing? How to Detect and Prove Fake Emails
Blog Overview – Imagine you open an email that looks like sent from the CEO of a company you work for. The tone is urgent. A wire transfer must go out immediately. Everything feels usual: name, logo, signature. But hours later money is gone. This is a situation where understanding what is email spoofing becomes unavoidable. It becomes evidence but what exactly does email spoofing mean, and why is it so dangerous? In this blog, we will understand what spoofing really is, how it works, and how to protect ourselves from it.
Why is Email Spoofing So Dangerous?

At its core, what is email spoofing? Email spoofing occurs when an attacker manipulates the “From” address in an email to make it appear as if the email is coming from a trusted or legitimate source. It’s a tactic to trick the recipient into opening an email, clicking on harmful links, or to download or check suspicious email attachments. In many cases, attackers manipulate the hidden technical areas like email headers. To the naked eye, everything appears completely normal. Under the hood, the fingerprints tell a different story.
Have you ever received an email message from the bank asking you to share all that crucial information, such as ATM PIN, account number, etc.? If yes, then you are at risk! This is because the bank never asks its clients to share such details; instead, it can be a spam email with a spoofed email ID. This is done just to convince the user to give sensitive information
How to Prevent Email Spoofing
Many people stop at the awareness tips. But awareness is just half the battle won. The real question is how to prevent email spoofing and what can be done about it. As email systems were built decades ago. The basic email protocol is SMTP. This does not verify the sender he/she claims to be. This weakness is what attackers exploit. One purpose behind email spoofing could be that the email spoofers may be attempting to “phish” the passwords as well as login names.
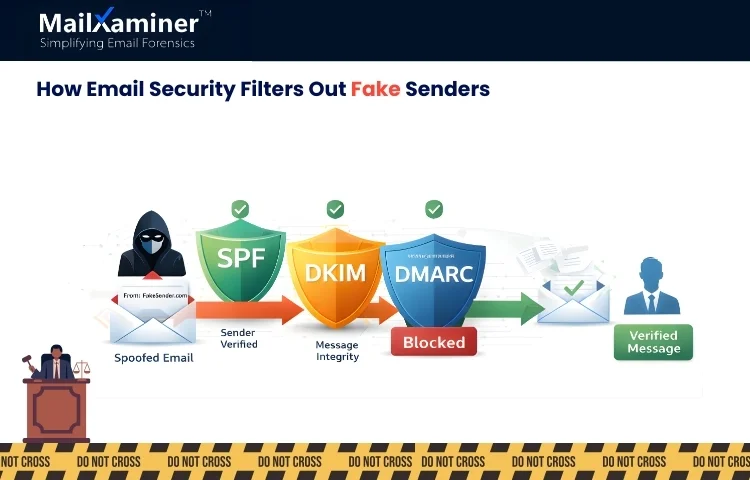
Now organizations use security checks like SPF, DKIM, and DMARC. We can think of these terms as a watchman checking identity cards before letting anyone in. They verify whether the sender is authorised or not. The truth is, even with these checks, spoofed emails still reach our inboxes. When any financial fraud or insider threat occurs. One needs evidence that is admissible in court.
How Email Spoofing Works Behind the Scenes
When we look at an email, normally. We only look at display names and addresses. Which can be thought of as the front desk. Behind that is the email headers (the control room).
Attackers can manipulate the “FROM” field. This manipulation allows cybercriminals to send spoofed emails that look convincingly legitimate, tricking recipients into taking harmful actions. But can not easily manipulate every technical trace. The header records routing paths, sending servers, timestamps, and IP addresses.
We can think of it as a flight path radar. An airline can paint the aircraft with friendly colors. But air traffic control can still track where the plane came from. In a forensic investigation, this metadata becomes an important part of the evidence.
Note – All the emails that seem to be dangerous at first glance are usually designed to trap the recipient into clicking on malicious links or downloading malware.
Many people confuse email spoofing and phishing; some consider it the same let’s look at the major difference between them.
Difference Between Email Spoofing and Phishing
You know what is email spoofing and let’s now see how it is different from phishing. They are both connected. But serve different areas in an attack. One focuses on identity manipulation and the other on deception of data theft. Let’s check out where they differ.
| Basis | Email spoofing | Phishing |
|---|---|---|
| Purpose | Forging the sender’s identity to appear legitimate. | Stealing sensitive information and login credentials. |
| What it changes | Manipulates the “From” address and email header details. | Alters content to trick and emotionally manipulate the victim. |
| Role in the attack | Used to disguise the attacker’s real identity. | Acts as a trap to capture data and exploit trust. |
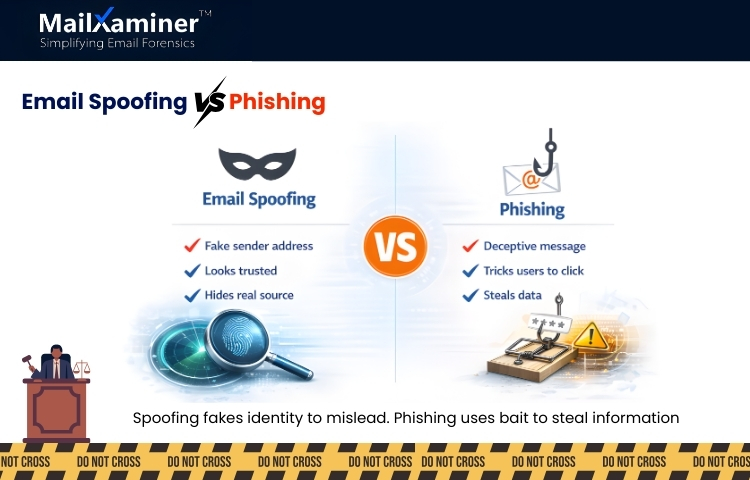
In a simple way, we can think of it like this. Spoofing makes email look trustworthy and professional. Phishing persuades the recipient to perform a harmful action.
Manual Detection Methods and Their Hidden Risks
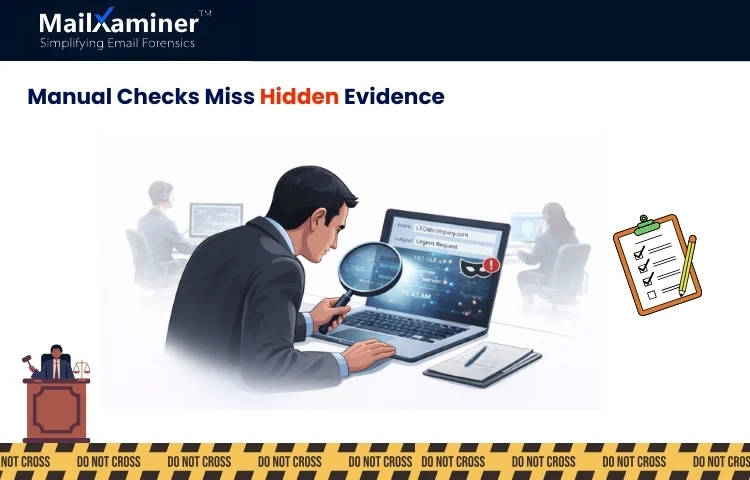
Now you know what is email spoofing. Let’s dig deeper into how we can check whether it is a spoofed email or a genuine one. We can manually check for headers. Many IT teams do this. We can:
- Open message source.
- Look at “Received” lines
- Compare domain spelling carefully
- Just hover over links, do not click them.
But here is the risk. When we inspect an email manually, we may not detect the same red flags. As manual investigation can be seen as a detective examining a crime scene without lab equipment. One may overlook tampering and fail to preserve evidence. In legal and corporate investigation missing even one technical element can weaken the entire case. For proper email analysis and an errorless approach, agencies and companies now prefer Email Forensics Software.
Why Email Investigations Fail Without Forensic Tools

In DFIR cases It is advisable to rely on the trusted software. This is so because we are in the era of different types of email threats like email spoofing, which can be used for financial fraud, data breach, etc. This is crucial for everyone involved in cybersecurity or digital forensics as investigators need to answer questions like.
- Is this email forged?
- Was it altered after its creation?
- Where it got originated?
- Is the evidence intact?
Without a structured forensics analysis, proving spoofing becomes difficult in court.
How Professional Tool Helps Unmask Spoofed Emails
Now you completely know what is email spoofing from a DFIR perspective. The goal is to find evidence. Tools like MailXaminer provide you with multiple features where investigators begin by examining email headers, and IP analysis helps reconstruct where the message actually originated rather than relying on the visible “From” field. To preserve integrity, methods of hash verification, such as MD5, act as a digital fingerprint. If the email changes, the fingerprint changes. This will ensure evidence remains intact.
Final Takeaway
So, how to prevent email spoofing? Use authenticated controls and train users. The investigator must ensure proper forensic capability when an incident occurs. With the help of proper tools, not only can spoofed emails be detected, but evidence can be found out, analysed, and presented in court.
Frequently Asked Questions
Q – What is email spoofing, and how can one recognize it?
Ans – It is when someone uses a fake sender’s address. One can recognize by checking the full email headers and verifying the real sending server.
Q – How prevent email spoofing and reduce risk?
Ans – To prevent email spoofing. Usage of email authentication methods, such as SPF, DKIM, and DMARC,with this one should always verify suspicious emails before responding.

